Apple And Government Official Are Battling Over The iPhone 5C Security
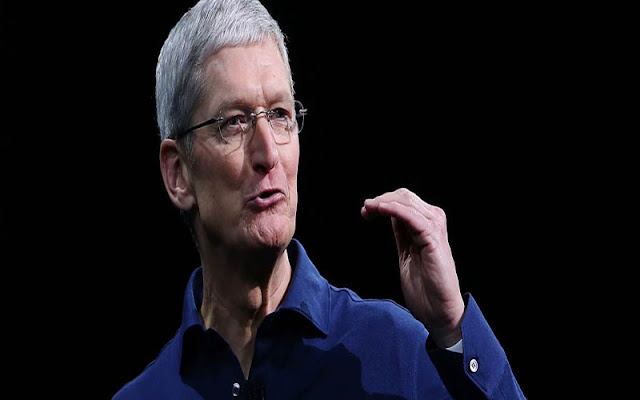
This week Apple is going to face a big test to its iPhone security. Apple is ordered by the Federal judge to assist the FBI regarding breaking into an iPhone which is owned by one of the shooters of San Bernardino. Whatever the CEO Tim Cook describes as a "dangerous" backdoor by which law enforcement can easily bypass the security code on an iPhone, all are actively opposing by the Apple.
There is a new feature in the Apple's latest iOS versions that if we attempt too many incorrect PIN entries then the iPhone completely wipe the data, and it can also delay attempts to guess PIN whenever we entered the incorrect PIN. These two features disable or prevent the FBI from brute forcing the iPhone 5c devices by trying to guess the code. And it has turned to Apple to get help.
The co-founder and CEO of independent information security firm Trail of Bits, Dan Guido has a believed that Apple can comply with the FBI's order because it is not a modern iPhone like (iPhone 5S or iPhone 6, 6S), it's a normal iPhone 5C device. Guido writes in his blog Post that
"I believe all of the FBI's requests are technically feasible,"
From past many years, Apple has been gradually making improvements in his iOS software security. Apple is also improving their features of pairing software by making advancements in hardware security. Touch ID concept for the first time has been introduced in iPhone by Apple along with so many unique features. Some of them are:
>> Security lock that's paired to a passcode.
>> It will also slow down attempts to guess PIN codes.
But these features are not present in Apple's iPhone 5C, it doesn't include Touch ID and Security Enclave. So, FBI is trying to make a number of PIN guesses on iPhone 5C as soon as possible.
Guido also argued that "For doing so, Apple has to create a special version of iOS to load onto the iPhone 5C, by which FBI able to guess one passcode within every 80ms,". But, Apple objected and said that "it will also open a door for hackers to achieve their target, and even they do so then there will not be any guarantee that the security code will be guess by FBI's tool".
As the nature of iOS is keep changing, it's likely that others or FBI have been able to use software flaws and other tools to gather information from devices. Even in latest iOS 9 release also there is lock screen security flaws. In previous iOS 8, there is no encryption of data like text messages or photos using a passcode.
Cryptographer Matthew Green speculates that
"Apple could have provided a passcode bypass in the past without breaking the passcode-encrypted data, simply because most of the data wasn't secured using the passcode."
It's already clear that FBI needs something different and unique from this iPhone 5C, and for the same Apple can also comply with code orders to supply data from iCloud. For Apple, it's difficult to comply with this kind of request because this device hardware tied to an improved encryption, and it's impossible for Apple to comply on devices with Touch ID.
Let see how this kind of issue can be solved by Apple and FBI. This is the main thing that's clearly troubling Apple. For this Apple has to weaken its encryption in order to provide FBI officials to gather the data, they need, along with a secure and protected way also, so that it can't be affected by any of the malicious attackers. It's a balance that tech companies and government officials around the world are battling over, even as President Obama receives his daily intelligence briefings on an iPad. Let see what will be the result of this battle.

0 comments:
Post a Comment
Note: only a member of this blog may post a comment.