Malware Found In Britney Spears Instagram Account.
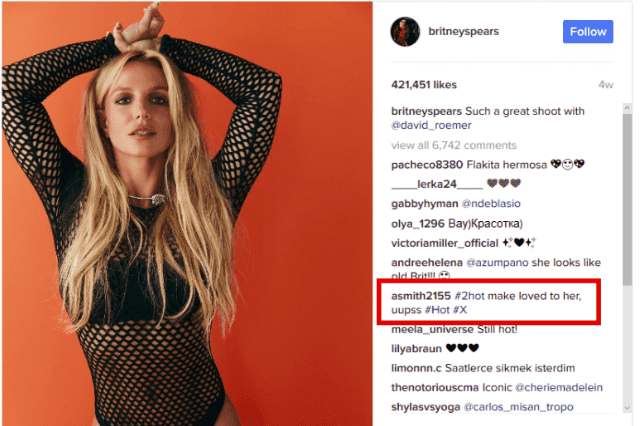
CyberSecurity researchers found the Malware in Britney Spears Instagram account, where attacker appeared malicious comment post in her account.
According to research, the Hackers group named TURLA behind the Malware, it's a Russian group known for targeting governments and officials. Cyber attackers spreading Malware through post the comment in world most famous singer Britney Spears Instagram account.
According to Eset, Malware was hidden in a Firefox browser extension. The extension uses a bit.[ly] URL to reach its C&C, but the URL path is nowhere to be found in the extension code. In fact, it will obtain this path by using comments posted on a specific Instagram post. The one that was used in the analyzed sample was a comment about a photo posted to the Britney Spears official Instagram account.
Technical analysis
This Firefox extension implements a simple backdoor. It will first gather information on the system it is running on and send it to the C&C, encrypted using AES. This is very similar to what the extension described in the Pacifier APT white paper is doing.The backdoor component has the ability to run four different types of commands:
- execute arbitrary file
- upload file to C&C
- download file from C&C
- read directory content – send a file listing, along with sizes and dates, to C&C
While we believe this to be some type of test, the next version of the extension – if there is one – is likely to be very different. There are several APIs that are used by the extension that will disappear in future versions of Firefox.
For example, it uses XPCOM to write files to disk and sdk/system/child_process to launch a process. These can only be used by add-ons that will be superseded by WebExtensions starting with Firefox 57. From that version onwards, Firefox will no longer load add-ons, thus preventing the use of these APIs.
Conclusion
The fact that the Turla actors are using social media as a way to obtain its C&C servers is quite interesting. This behavior has already been observed in the past by other threat crews such as the Dukes. Attackers using social media to recover a C&C address are making life harder for defenders. Firstly, it is difficult to distinguish malicious traffic to social media from legitimate traffic.Secondly, it gives the attackers more flexibility when it comes to changing the C&C address as well as erasing all traces of it. It is also interesting to see that they are recycling an old way of fingerprinting a victim and finding new ways to make the C&C retrieval a bit more difficult.

0 comments:
Post a Comment
Note: only a member of this blog may post a comment.